All you need to know about credential stuffing
The term "credential stuffing" was coined by Sumit Agarwal, a former Deputy Assistant Secretary of Defense under President Obama. In 2011, while working at the Pentagon, Deputy Assistant Secretary Agarwal discovered that hackers began using surnames and passwords stolen from one site to gain access to other sites. These attacks are currently a massive problem and they started to happen more often during COVID-19 pandemic. How to prevent and defend against it?
Credential stuffing, one of the top threats for web
If you are one of the person who has the same username and a password for many websites you are in big trouble. Credential stuffing become on of the top threats for web mainly because instead of trying to guess passwords, attackers use lists of known valid credentials which they obtain from various data breaches. This method is, unfortunately for us, far more successful due to reusing of passwords across different websites by many people. In order to make the breach more profitable, attacks are automated and performed at scale. In the last couple of years, hackers gained access to billions of login credentials which are now used for spam, phishing and account takeovers.
How big is the problem? It's BIG
Though in the past credential stuffing was not such a big deal, now the problem is pervasive. Between November 2017 and March 2019, security and content delivery company Akamai detected 55 billion credential stuffing attacks, which means that every single day there were more than 115 million attempts! In the Verizon Data Breach Investigations Report (DBIR) from 2019 we can find the info that credential stuffing was used in 29% of all data breaches. Nearly 9 billion compromised credentials are currently put up for sale in Dark Web for as little as $2, depending on the service or website. Credential stuffing attacks are a serious threat for ALL online activities with banking and social apps being targeted the most--costing cost US businesses over $5 billion each year(!). One of the biggest cases of credential stuffing include HSBC incident (in 2018 data breach affected about 14,000 of its customers) and Dunkin' Donuts case (there were two incidents, in 2018 and 2019, that affected 1,200 of their clients).
We know how to defend against it
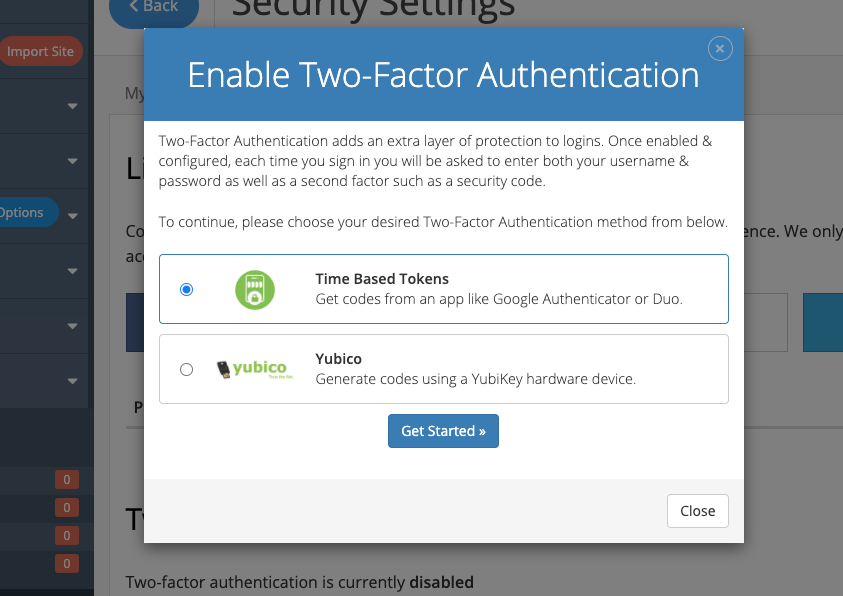
Start with changing your passwords. The best way to set unique and strong passwords is to use a password manager. Changing all passwords may be time consuming, but if you do it, you will be no longer a potential victim of credential stuffing. Second step is enabling two-factor/multifactor authentication on every account where it is available. You can set up Two-Factory Authentication specifically for your Joomla or WordPress website. We also highly recommend turning on Two-Factory Authentication in your Cloud Control Panel account. To do that simply visit Security Settings tab in your profile options. In addition to these steps, you can also use a detection tool that will help you identify risk signals such as a failed authentication attempt.
Although credential stuffing is here to stay, we now know how to successfully detect and defend against it. The main goal is to make obtaining credentials as difficult as possible by using all known tools. Awareness is our strength so we need to remember that reusing of a given password across multiple accounts is very dangerous and it's a matter of time when it will be compromised.